Why Kaspersky’s Bank Robbery Report Should Scare Us All
So, you don't work for a financial institution? Don't think you're off the hook for this level of theft. Banks are certainly not the only organizations moving around massive amounts of money every day.
be fired for embezzlement before anyone ever caught on that we weren't the guilty parties? That scares me. And I think it should scare you, too.
There's nothing new about the fact that the exploit involved an old Microsoft Office vulnerability for which a patch had long since been issued. We already know many organizations are sloppy when it comes to patch updates.
But the level of targeting – heck, let's call it stalking – that was involved in this attack seems pretty sophisticated to my untrained eye. The Kaspersky report noted that, as part of an automated reconnaissance phase, "the Carbanak malware checked victim systems for the presence of specialized and specific banking software. Only after the presence of these banking systems was confirmed were victims further exploited."
[ What did the Anthem breach teach us? Read Anthem Hack: Lessons For IT Leaders. ]
So, where does that leave enterprise IT, and others in your organization? Well, for starters, whatever education we're giving employees about how to identify potential malware can't possibly account for this kind of advanced persistent threat (APT). As Kaspersky stated in its report:
We believe that the Carbanak campaign is a clear indicator of a new era in cybercrime in which criminals use APT techniques directly against the financial industry instead of through customers. APTs are not only for stealing information anymore.
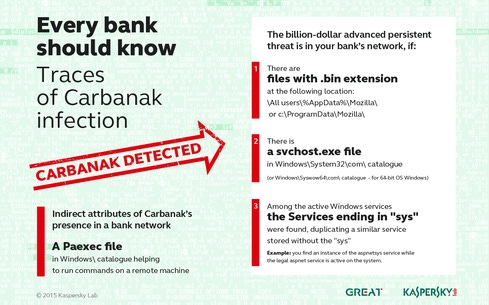
Here's some advice from Kaspersky on the early warning signs that Carbanak has hacked you:

(Image: Courtesy of Kaspersky Lab)
Sure, at the moment, the targets were financial institutions. It's really a high-tech version of cooking the books. Once the hackers were inside, according to Kasperksy, they were able to set up fake accounts, or add dollar amounts to real accounts, and then authorize the transfer of those sums out of the bank, either to ATM machines or to external accounts, without anybody catching on.
So, you don't work for a financial institution? Don't think you're off the hook. Banks are certainly not the only organizations moving around massive amounts of money every day. All major multinational corporations and government agencies could, potentially, have their finance and accounting systems fall prey to a similar attack.
According to Krebs:
Most organizations — even many financial institutions — aren't set up to defeat skilled attackers; their network security is built around ease-of-use, compliance, and/or defeating auditors and regulators. Organizations architected around security (particularly banks) are expecting these sorts of attacks, assuming that attackers are going to get in, and focusing their non-compliance efforts on breach response.
Have I scared you yet? If not, tell me why. And, if you are as terrified as I am, tell me how you plan to address this in your organization. Let's discuss in the comments section below.
Attend Interop Las Vegas, the leading independent technology conference and expo series designed to inspire, inform, and connect the world's IT community. In 2015, look for all new programs, networking opportunities, and classes that will help you set your organization’s IT action plan. It happens April 27 to May 1. Register with Discount Code MPOIWK for $200 off Total Access & Conference Passes.
About the Author(s)
You May Also Like







