A report from a security firms finds that Samsung's smartphones are vulnerable to attacks thanks to replacement software in the SwiftKey keyboard. However, it's not really Samsung's fault.

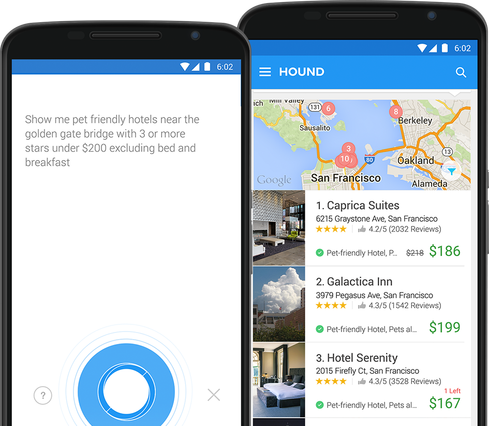
10 Smartphone Apps You Can Talk To
10 Smartphone Apps You Can Talk To (Click image for larger view and slideshow.)
Security research firm NowSecure says it has uncovered a serious problem in all of Samsung's smartphones that may allow them to be attacked, according to some published reports.
This vulnerability comes from the SwiftKey keyboard replacement software included with all of the phones, rather than from the core system software.
The problem seems to be that the software, which is given system-level access by Samsung, updates itself in plain text. This means that an attacker can spoof SwiftKey into thinking it is getting an update when it is really being attacked.
This attack could then run malicious code that could access the camera and microphone sensors or eavesdrop on phone calls.
NowSecure says it notified Samsung in December 2014 of the vulnerability, and a patch was developed in early 2015.
However, the patch needs to be deployed by the wireless carriers, rather than the user. Since no one knows if the patch has in fact been deployed by the carriers, one must assume the vulnerability is still extant.
NowSecure has said that Verizon Wireless, Sprint, and AT&T have not deployed it, according to their tests.
Users would be most vulnerable to a spoofing attack on insecure networks like public WiFi hotspots.
Paco Hope, principal consultant with Cigital, a consulting firm that looks at application and software security, wrote in June 17 statement that this flaw with Samsung's smartphones shows that companies need to do more than testing to find flaws in their software.
"This Samsung vulnerability is a textbook example of a software vulnerability in the design, not the code," Hope wrote. "The operating system updates a core component over HTTP and verifies it with a simple hash also loaded over trivially hijacked HTTP. It is easy to forge an arbitrary replacement. Software security techniques like threat modeling and architecture risk analysis pick up obvious security anti-patterns like this. There are many valid secure design patterns that would have served. This is an example of why software security involves a lot more than penetration testing and code review.
[Read about millennials and security.]
While Hope makes a valid point, it is also obvious that Samsung got hosed by SwiftKey here.
Samsung probably did not know about SwiftKey's updating practices before giving it system-level access. So, the upshot of this will be more scrutiny for the software partners of all brands of phones.
When it comes to smartphone security, Samsung isn't the only vendor reporting trouble lately.
In May iPhone users were plagued by a string of texts that could crash the device. Although Apple offered a temporary fix after several users and security firms reported the problem, there hasn't been a permanent fix just yet. However, there doesn't seem to be any long-term damage from this particular flaw.
[Editor's note: Due to an editing error, the number of samsung phones affected was mistated. The estimated number is actually 600 million, according to NowSecure.]
About the Author(s)
You May Also Like







